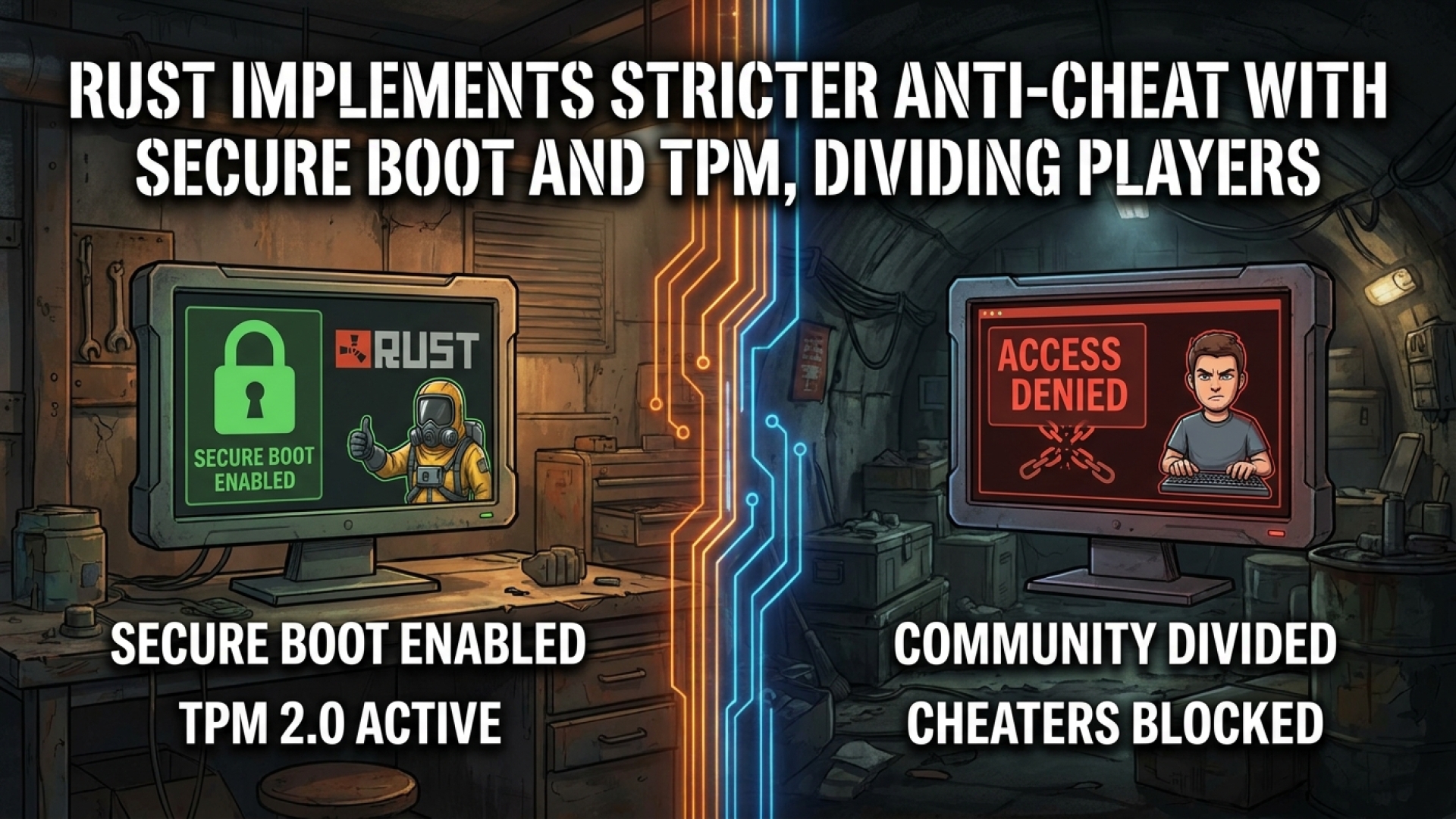
In the high-stakes world of survival gaming, few titles evoke as much passion—and frustration—as Rust. At Digital Tech Explorer, we’ve tracked the evolution of digital security and how it intersects with user experience. Recently, Facepunch Studios took a definitive stand in the ongoing arms race between developers and cheaters. By implementing Secure Boot and Trusted Platform Module (TPM) requirements, Rust is transitioning into a new era of hardware-level security.
The Technical Shift: TPM 2.0 and Secure Boot
As a software engineer-led platform, we recognize that software-based anti-cheat often falls short against sophisticated exploits. Facepunch COO Alistair McFarlane recently announced that starting this March, Rust server owners have the option to enforce TPM 2.0 and Secure Boot. While currently an opt-in feature, this is a clear signal of what’s to come. McFarlane noted that this phase allows the team to gather essential metrics before a potential mandatory rollout across the entire gaming ecosystem of the title.
For those unfamiliar with the hardware side of things, TPM 2.0 is a dedicated microcontroller designed to secure hardware through integrated cryptographic keys. When combined with Secure Boot, it ensures that only trusted software can execute during the system startup process, making it significantly harder for “kernel-level” cheats to hide from detection.
| Security Feature | Function | Impact on Cheating |
|---|---|---|
| TPM 2.0 | Hardware-based security key storage. | Prevents hardware ID spoofing and secures identity. |
| Secure Boot | Verifies digital signatures of OS loaders. | Blocks unauthorized “rootkit” style cheats from loading at startup. |
| Kernel-Level Anti-Cheat | Deep system monitoring during gameplay. | Detects real-time manipulations in system memory. |

A Necessary Standard in Competitive Gaming
This move isn’t happening in a vacuum. At Digital Tech Explorer, we’ve seen a growing trend where top-tier PC games are demanding deeper system access to maintain integrity. Modern titles like Highguard, Battlefield 6, and Black Ops 7 have normalized these protocols. While invasive, kernel-level strategies are currently the most effective deterrent against modern cheating software.
However, this security comes with trade-offs. The requirement for TPM and Secure Boot is a primary reason why Rust continues to struggle with compatibility on Linux and Valve’s Proton layer. For enthusiasts of open-source hardware configurations, these barriers remain a significant point of contention.

Community Insight: Security vs. Accessibility
The feedback from the Rust community highlights a classic tech dilemma: security versus accessibility. Our analysis of player sentiment shows a deep divide. On one hand, players who have invested thousands of hours into the game are eager for any measure that reduces the frequency of aimbots and wallhacks. Reddit user Shot-Buy6013 echoed this, noting that anyone serious about the game’s health should support the reduction of exploits.
Conversely, there is a valid concern regarding the “digital divide.” Users like psychoPiper pointed out that mandatory hardware requirements can alienate players who cannot afford to upgrade to newer motherboards or processors. It’s a delicate balance that Facepunch must strike as they move forward.
The Road Ahead for Rust
As TechTalesLeo, I see this not just as a software update, but as a story of a developer fighting to preserve the soul of their creation. Facepunch’s commitment to a fairer environment through TPM 2.0 and Secure Boot aligns Rust with the most secure 2024 releases and beyond. While the transition may be rocky for some, the goal is a more transparent and equitable playground for every survivalist.
Stay tuned to Digital Tech Explorer for further deep dives into how AI acceleration and emerging security tech are changing the way we play. Our mission is to keep you ahead of these trends, ensuring you have the knowledge to navigate the evolving tech landscape.
Disclaimer: All content on Digital Tech Explorer is for informational and entertainment purposes only. Some links may be affiliate links, meaning we may earn a commission at no additional cost to you.