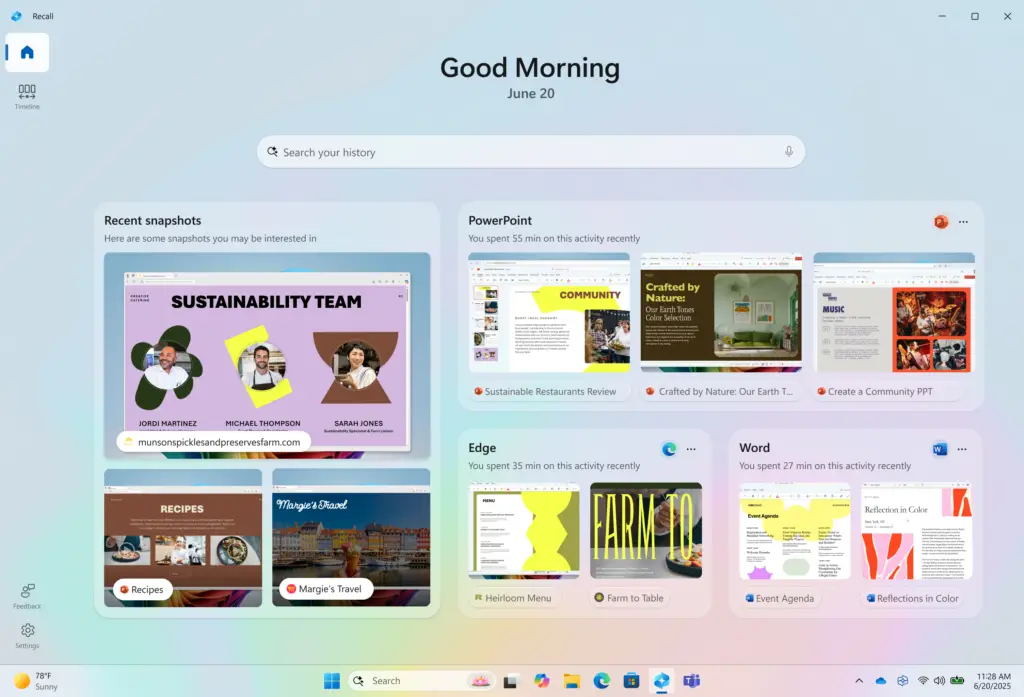
The saga of Windows Recall continues to unfold, serving as a cautionary tale for the 2024 tech landscape. Originally envisioned as a revolutionary AI feature that screenshots your PC activity to create a searchable timeline, Recall’s journey has been plagued by delays. After several “recalls” of its own due to significant cybersecurity concerns, Microsoft redesigned the architecture. However, as we keep a close eye on these developments here at Digital Tech Explorer, new reports from the research community suggest that the underlying risks may not be as “fixed” as we hoped.
While Windows Insiders have had access to the refreshed Recall for months, security researcher Alexander Hagenah has already demonstrated that the more things change, the more the vulnerabilities remain. Hagenah, who previously identified flaws in the original version, has developed a new tool that exposes how the redesigned Recall captures and potentially exposes data. This discovery, first reported by The Verge, highlights a persistent gap in Microsoft’s “locked box” approach to user privacy.

Unpacking the Security Claims Behind the “Locked Box”
Microsoft’s defense of Recall’s security model rests heavily on its September 2024 architectural update. The company claims that all snapshots and metadata are shielded by VBS Enclaves—virtualized environments designed to isolate sensitive data. In theory, this information remains in a secure vault that only opens when the user provides explicit permission via Windows Hello biometrics.
However, Hagenah’s research suggests a narrative of false security. “My research shows that the vault is real,” he notes, “but the trust boundary ends too early.” This means that while the data is safe while sitting still, the process of accessing and displaying it creates a window of opportunity for malicious actors.
TotalRecall Reloaded: How the Exploit Works
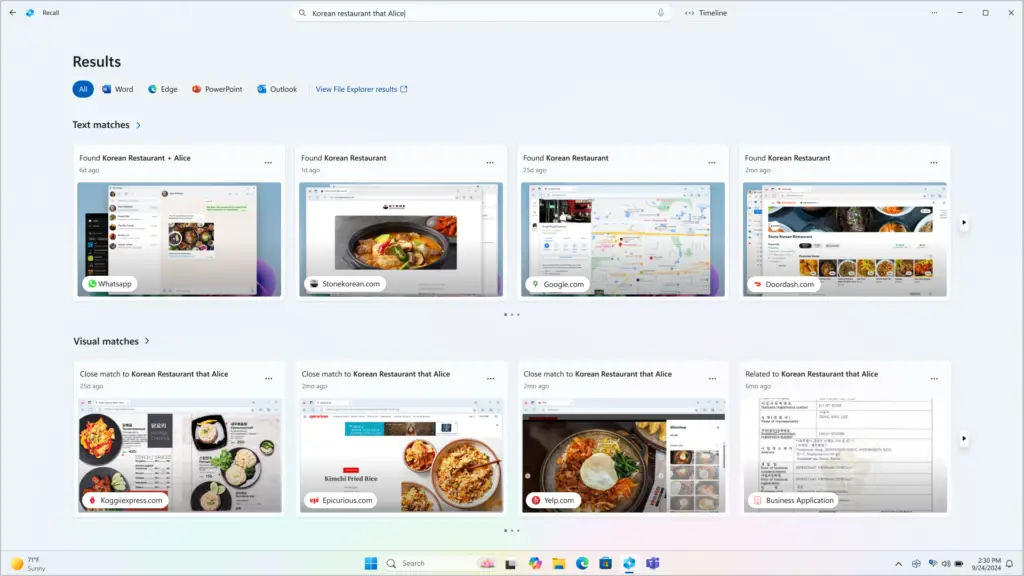
The tool Hagenah developed, dubbed TotalRecall Reloaded, operates with a deceptive simplicity that should concern any hardware enthusiast or professional. The software sits quietly in the background of the OS, waiting for the user to legitimately open the Recall timeline. Once the user clears the Windows Hello prompt, TotalRecall Reloaded “rides along” with that authorized session to scrape the decrypted contents of the vault.
This is exactly the type of “malware ride-along” Microsoft claimed its architecture would prevent. By leveraging the user’s own authentication, the tool can extract browsing history, private emails, and sensitive messages that have appeared on the screen, bypassing the intended protections.
Microsoft’s Stance: A Feature, Not a Vulnerability?
In a surprising twist, Microsoft has downplayed the findings. After Hagenah responsibly disclosed his research, the company stated that the behavior does not constitute a security vulnerability. David Weston, Microsoft Security’s corporate vice president, told The Verge that the access patterns are “consistent with intended protections” and that existing controls like authorization timeouts and “anti-hammering” protections are sufficient to limit abuse.
For those of us tracking AI acceleration and its impact on privacy, this response is polarizing. From Microsoft’s technical perspective, the system is performing exactly as coded: it decrypts data when the user asks it to. The fact that another process can see that decrypted data during the authorized window is viewed by Microsoft as a side effect of how operating systems handle rendering, rather than a break in the “titanium vault.”
Hagenah’s assessment remains blunt. While he praised the VBS Enclave as being technically “rock solid,” he pointed out the fundamental flaw in the workflow. “The vault door is titanium. The wall next to it is drywall,” he explained. By sending decrypted content to an unprotected process for rendering, the system effectively leaves the back door open once the front door is unlocked.
As we continue to explore the boundaries of digital innovation here at Digital Tech Explorer, the Recall controversy serves as a reminder that robust encryption is only as strong as the interface it serves. For now, users must decide if the convenience of an AI-powered memory is worth the risk of a “drywall” security boundary.

